
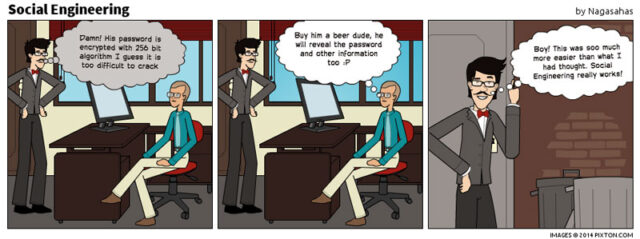
Social engineering could be interpreted as an art of manipulating. Criminals are seeking different types of information. If you are the target, criminals try to trick you to give them your credit card number, passwords of different websites you use, or even hack your computer and take control. They use this tactics because its easier to trick people to trust then to find ways to hack your password. In virtual world, you should know when and when not trust a person or take them by their word. Even when you are on telephone if you are not sure the person you’re speaking with is legitimate, you better not provide personal information or any kind of info. It’s just another form of hacking. But, social engineering is actually nothing new. Its a two sided sword. Because while technology is helping new frauds getting caught, it also created new path opportunities for frauds.
Honestly, it doesn’t matter how many locks you have on door, security alarm systems, fences or dog guards, if you let that fake pizza delivery men inside without checking if he’s legit, this way you are completely open to all the risks he represents.
There are many various types of attacks of social engineering. It can be done through e-mail. Imagine someone hacks your mail and inside you have different passwords for all kinds of websites or even more sensitive information like your credit cards number. Criminal can get inside your computer with creating a virus. The technique requires creating a RAT, which is form of virus that is implemented in picture, audio, video file, or could be uploaded online. Then a person opens link and gets directed automatically to other page and not even knowing that when clicked, criminal got the pass to your PC. Or if you download the file and click on it happens the same. Those kinds of viruses are made so good that it’s almost impossible for most of the antivirus apps to discover them and notify the victim on time.
Theres also scenario which is called Phishing. It can contain a text that looks like it’s coming from some popular and legit company, bank, institution or even school. Messages can also state that you’re the winner of some lottery, requiring you to fill important information. On torrent sites, the method that is used a lot is called baiting. If a new movies comes out there’s gonna be many downloads, but uploader, in this case criminal, can put a virus inside and when you play movie – you downloaded virus on your system . On Ebay and other selling sites there have been many frauds, listing products for sale and when you buy they never ship you product, be aware to look for sellers rating and comments from other buyers.

Here’s an interesting example where social engineering has prevailed over time where there is no advanced technology. The classic example comes from the story of famous ” Trojan ” horse from ancient Greece. After unsuccessfully fighting the war for 10 years, Greek army soldiers appeared to gave up the battle. So they thought of making a big wooden statue of horse as a gift of saying that they lost and Troy won. What they didn’t know is that there was small amount of Greek soldiers inside horse. The Troyan people moved horse inside, started to drink, eat and celebrate. Greek soldiers quietly got out from horse and opened the city gates so that the rest of Greek army can join in. You can guess, Greek soldiers destroyed the city of Troy.
So, be careful, don’t become just another victim of fraud. Research the facts and slow down before clicking on suspicious links, especially don’t download link from someone who looks suspicious and of course you would want to make sure you have good antivirus program installed on your PC to protect yourself. Below, you can check out the infographic in which you can find more information about social engineering:














